-
Founded in August 2005 with a vision to systematically change the IT approach and support within Trinidad and Tobago.
-
We specialize in many different areas including Email Archiving Systems, Document Management Systems, EndPoint Protection Solutions, Backup Solutions, Remote Management, Cyber Security Solutions, Virtualization and Multi Factor Authentication.
-
What is CADI?
The Ideal Solution looking at all aspects of your IT Infrastructure.Createx Active Defense Infrastructure or CADI is a revolutionary solution designed and implemented by Createx Limited for businesses who are open to new & emerging threats. Using enterprise solutions and products supported by our partner and alliance networks we are able to create a solutions for all markets (Small, Mid -Size, Large companies).
-
Modules
CADI includes various modules- Service Level Agreements (Active Support System)
- An Enterprise Security Appliance (Includes Firewalls, VPN, Spam, Web Control, Internet Redundancy, Site to Site Remote Connections, etc.)
- Wireless Security
- 2 Factor Authentication (2FA)
- Endpoint Security (Antiviral, Ransomware, Web, Device Control etc.)
- Cloud Backup Solutions (3-2-1 Backups with 256 Bit SSL Encryption)
- Disaster Recovery (DR) Systems
- Document Management Systems (DMS)
- Virtualization
- Remote Monitoring & Management (RMM)
- ICT (Information & Communication Technologies) Policy Creation and Development
- Infrastructure Creation, Development and Documentation
-
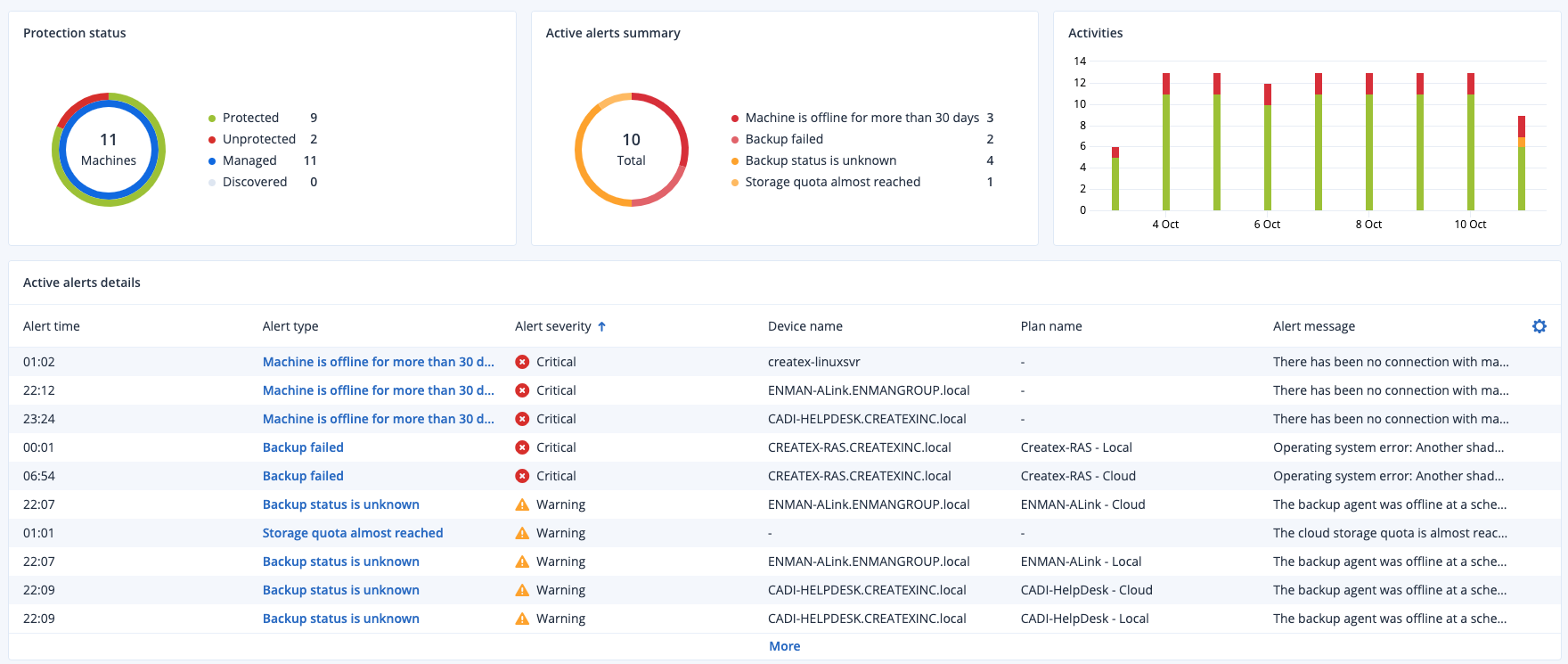
RMM
CADI with RMM (Add-on)- Dashboard Notifications
- RealTime Alerts
- Patch Management
- Reporting
Call for more details.
- Dashboard Notifications
-
Pricing
Quotation Required, Prices may vary depending on the organization's size and requirements. Call for more details.
- What is Intercept X?
- What is Intercept X with EDR?
- What is Intercept X with XDR?
- What is Intercept X with MDR?
- Pricing
-
What is Intercept X?
Sophos Intercept X Hightlights- The #1 rated malware detection engine, driven by deep learning
- Exploit prevention stops the techniques attackers use to control vulnerable software
- Active adversary mitigation prevents persistence on machine
- Root cause analysis lets you see what the malware did and where it came from
- Ransomware specific prevention technology
- Intercept X augments your existing antivirus deployment. Intercept X Advanced replaces your existing endpoint security by combining modern techniques with foundational approaches.
Sophos Intercept X stops the widest range of attacks with a unique combination of deep learning malware detection, exploit prevention, anti-ransomware, and more.
-
What is Intercept X with EDR?
Intelligent Endpoint Detection and Response (EDR)
The first EDR designed for security analysts and IT administrators
Intercept X Advanced with XDR allows you to ask any question about what has happened in the past, and what is happening now on your endpoints. Hunt threats to detect active adversaries, or leverage for IT operations to maintain IT security hygiene. When an issue is found remotely respond with precision. By starting with the strongest protection, Intercept X stops breaches before they start. It cuts down the number of items to investigate and saves you time.
- The strongest protection combined with powerful EDR
- Add expertise, not headcount
- Built for IT operations and threat hunting
-
What is Intercept X with XDR?
Extended Detection and Response (XDR)
Intercept X Advanced with XDR goes beyond the endpoint, pulling in rich network, email, cloud and mobile* data sources to give you an even broader picture of your cybersecurity posture. You can quickly shift from a holistic view down into granular detail. For example:
- Cross reference indicators of comprise from multiple data sources to quickly identify, pinpoint and neutralize a threat
- Use ATP and IPS events from the firewall to investigate suspect hosts and identify unprotected devices across your estate
- Understand office network issues and which application is causing them
- Identify unmanaged, guest and IoT devices across your organization’s environment
-
What is Intercept X with MDR?
Managed Threat Response (MDR)
- Threat Hunting - Proactive 24/7 hunting by our elite team of threat analysts. Determine the potential impact and context of threats to your business.
- Response - Initiates actions to remotely disrupt, contain, and neutralize threats on your behalf to stop even the most sophisticated threats
- Continuous Improvement - Get actionable advice for addressing the root cause of recurring incidents to stop them for occurring again
-

Pricing
Quotation Required, Prices may vary depending on the organization's size and requirements. Call for more details.
-

Whats is Cybersecurity?
Cybersecurity is the practice of protecting systems, networks, and programs from digital attacks. These cyberattacks are usually aimed at accessing, changing, or destroying sensitive information; extorting money from users; or interrupting normal business processes.
Implementing effective cybersecurity measures is particularly challenging today because there are more devices than people, and attackers are becoming more innovative. -

How can we help?
Improve your IT Infrastructure with our Cybersecurity Solutions.Our systems work with all company sizes from Home to Enterprise Solutions. Purchase or lease anyone of our solutions. Full Integration with our previous CADI System*.
Ask for a Demo
For more information and pricing contact us.
*Certain conditions may apply.
-

Email Archiving Systems
Archive multiple Email Accounts which are over capacity or running out of Email Storage. Secure access to Old Emails at anytime with an Enterprise storage solution. Reduce cost of email subscriptions. -

Microsoft 365
Microsoft 365 (often called Microsoft Office 365 or Office 365) is a Web-based version of Microsoft's Office suite of enterprise-grade productivity applications. Office 365 is delivered to users through the cloud and includes Exchange Online for email, SharePoint Online for collaboration, Lync Online for unified communications, and a suite of Office Web Apps, Web-based versions of the traditional Microsoft Office suite of applications. The Application may also be installed on the users computer depending on the solution choosen. -
Createx Cloud
- Perform local and offsite cloud backup in one easy step.
- Back up everything — disks, partitions, servers, data — to the Createx Cloud.
- Recover anything quickly and easily — files, folders, applications, or an entire system.
- Keep backups safe in Createx’s ultra-secure, Tier-IV designed & SSAE-16 compliant local data centers.
-

Sophos Intercept X
Features- Intelligent Endpoint Detection
- Add expertise, not headcount
- Guided incident response
- End-to-End Endpoint Protection
- Exploit Prevention
- Malware Cleanup
- Synchronized Security
- Sophos Central
- Intelligent Endpoint Detection and Response (EDR)
- Extended Detection and Response (XDR)
- Managed Threat Response (MTR)
-
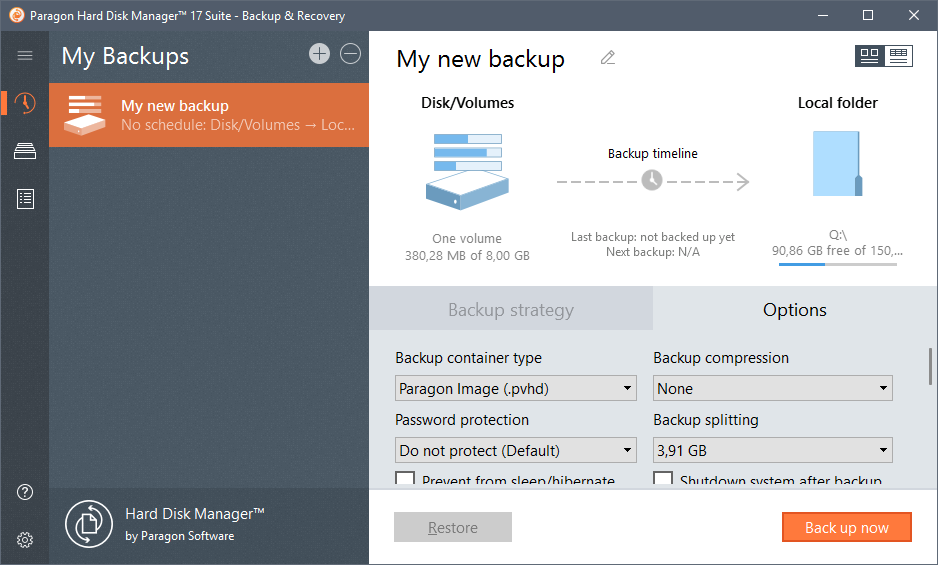
Paragon Hard Disk Manager 17
Key Features- Backup and Recovery data
- Migrate OS
- Partition disks
- Erase disks









